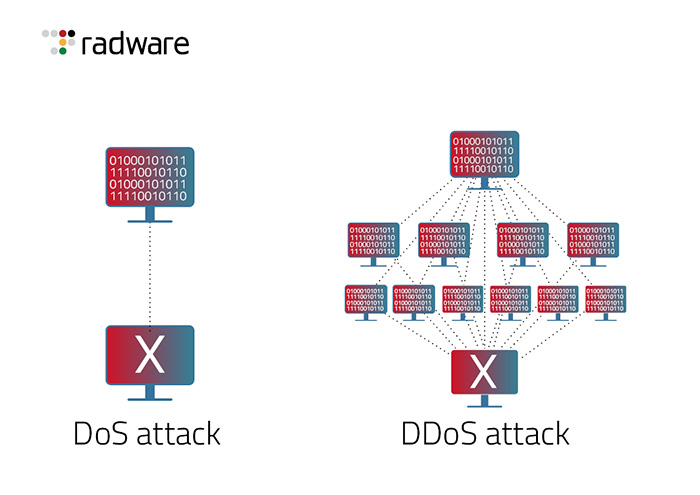
How to Help Protect Dynamic Web Applications Against DDoS Attacks by Using Amazon CloudFront and Amazon Route 53 | AWS Security Blog
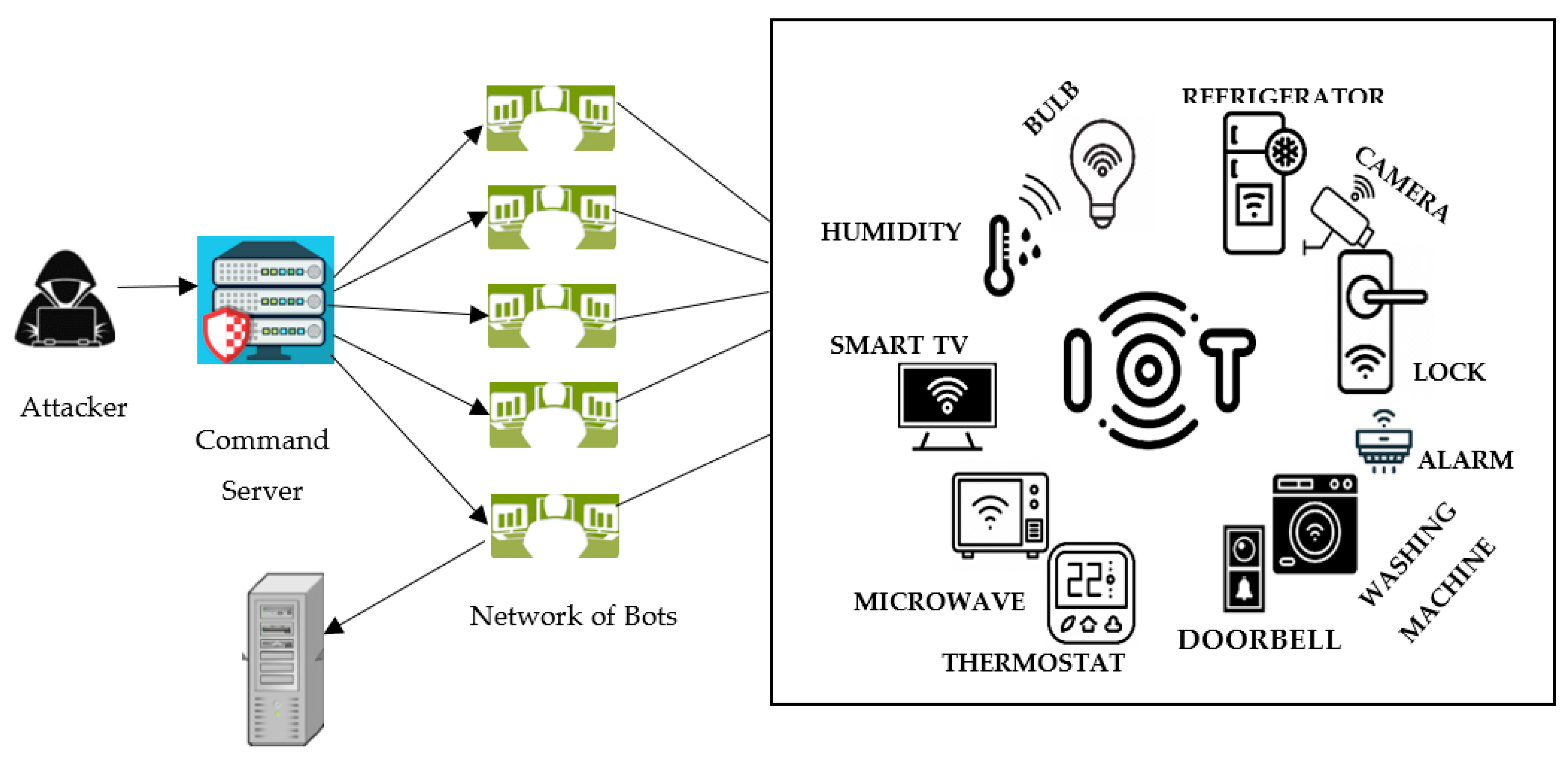
Applied Sciences | Free Full-Text | A Lightweight Model for DDoS Attack Detection Using Machine Learning Techniques